APIs are the silent heroes of modern apps. They connect services. They move data. They make login buttons, payment pages, and mobile apps work. But they are also a favorite target for attackers. If an API is exposed, your data is exposed. That’s why real-time API security platforms matter so much today.
TLDR: APIs power modern apps, but they are a major security risk if left unprotected. Real-time API security platforms monitor traffic, detect threats, and stop attacks before damage happens. Like Noname Security, tools such as Salt Security, Traceable AI, Cequence Security, and Data Theorem help companies discover, test, and protect APIs automatically. They offer visibility, threat detection, and fast response all in one place.
Think of APIs like doors in a large office building. Some are front doors. Some are side doors. Some are hidden in the back. You need to know where all the doors are. And you need guards watching them 24/7.
That’s where API security platforms come in.
Let’s look at four strong alternatives to Noname Security that help protect APIs in real time.
1. Salt Security
Salt Security focuses heavily on API discovery and threat detection. It is designed to automatically find APIs across cloud environments, on-prem systems, and hybrid setups.
Many companies do not even know how many APIs they have. Some are old. Some are forgotten. Some were built fast and never updated.
Salt fixes this.
What It Does Well
- Automatic API discovery across your entire environment
- Behavior-based threat detection
- Attack prevention in real time
- Detailed risk scoring for each API
Instead of just blocking known bad IP addresses, Salt watches behavior. It learns what “normal” looks like. When something strange happens, like a user requesting thousands of records very fast, it raises a flag.
This approach is powerful because many API attacks use valid credentials. The hacker logs in like a normal user. But then they abuse the system.
Salt catches that unusual behavior early.
Why it’s useful: It gives security teams deep visibility without slowing developers down. It works quietly in the background and alerts you before small issues become major leaks.
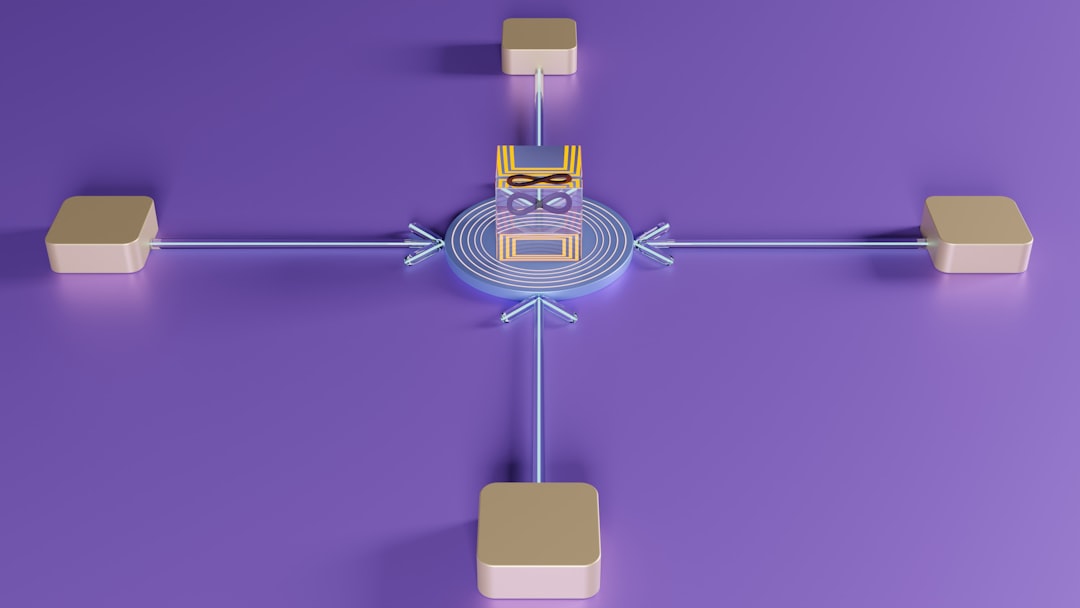
2. Traceable AI
Traceable AI takes observability to the next level. It maps every API. Every service. Every connection.
Think of it like a live GPS system for your APIs.
If something moves wrong, you know instantly.
Core Features
- Full API inventory and mapping
- Real-time threat detection
- Bot and abuse protection
- CI/CD pipeline integration
Traceable integrates directly into Kubernetes, cloud environments, and microservices architectures. That makes it perfect for modern DevOps teams.
It also connects with your development lifecycle. This means vulnerabilities can be detected before they reach production.
That’s a big deal.
Fixing a problem during testing is cheap. Fixing it after a breach is expensive. Very expensive.
Traceable uses AI and machine learning to understand traffic patterns. If an API suddenly begins leaking too much data, or responding in unusual ways, alerts are triggered immediately.
This makes it ideal for fast-growing startups and large enterprises alike.
3. Cequence Security
Cequence Security focuses strongly on API abuse and bot attacks.
Not all API threats look like classic hacks. Some are automated bots scraping data. Some test login credentials repeatedly. Some try to exploit business logic flaws.
Cequence specializes in stopping those hidden threats.
Key Capabilities
- API attack detection and prevention
- Advanced bot mitigation
- Business logic abuse detection
- Real-time blocking
One standout feature is its focus on protecting revenue. For example, if attackers try to exploit discount logic or reward systems, Cequence detects that pattern.
This is important for e-commerce, fintech, and SaaS companies.
APIs often power checkout pages, loyalty programs, and partner integrations. If attackers manipulate those, companies lose money quickly.
Cequence provides detailed analytics dashboards. Security teams can see attack sources, frequency, and targeted endpoints.
That visibility helps companies make smarter decisions about rate limiting, authentication policies, and API design.
Simple idea: Stop automated abuse before it turns into fraud.
4. Data Theorem
Data Theorem offers end-to-end API security. It combines discovery, testing, and runtime protection into one system.
It focuses heavily on risk reduction and compliance.
This makes it especially appealing for healthcare, finance, and government organizations.
Main Features
- Continuous API discovery
- Automated security testing
- Runtime protection
- Compliance reporting tools
Data Theorem doesn’t just monitor live traffic. It also analyzes API configurations and source code integrations.
This layered approach reduces blind spots.
For example, it can detect:
- Exposed sensitive data fields
- Weak authentication implementations
- Misconfigured endpoints
- Shadow APIs
Shadow APIs are APIs that exist but are not documented. They are dangerous because security teams do not track them.
Data Theorem helps uncover those hidden risks.
Its compliance reporting also simplifies audits. Instead of scrambling during review time, companies can generate real-time reports.
That saves time and reduces stress.
Why Real-Time Protection Matters
Old security methods relied on static rules.
Block this IP. Patch that vulnerability. Update once a month.
But API threats move fast.
Attackers automate everything. They scan systems in seconds. They test endpoints nonstop.
Real-time API security platforms work differently. They:
- Monitor traffic continuously
- Analyze behavior patterns
- Detect anomalies instantly
- Block or limit suspicious activity
- Alert teams immediately
This live monitoring is essential.
Without it, companies often discover breaches weeks or months later.
By then, the damage is done.
What to Look for in an API Security Platform
Choosing the right tool depends on your environment. But some must-have features are universal.
1. Full API Discovery
You cannot protect what you cannot see.
2. Behavior-Based Detection
Credential-based attacks are common. The system must detect unusual usage patterns.
3. Integration with DevOps
Security should not slow development. It should support it.
4. Real-Time Response
Detection is not enough. The system must act fast.
5. Clear Reporting
Security data must be easy to understand. Dashboards should be simple, not overwhelming.
Final Thoughts
APIs are growing rapidly. Every mobile app. Every SaaS platform. Every smart device relies on them.
But growth increases risk.
Platforms like Salt Security, Traceable AI, Cequence Security, and Data Theorem provide strong protection similar to Noname Security.
They discover APIs automatically. They monitor traffic. They detect threats. They block attacks in real time.
And most importantly, they help teams sleep better at night.
API security does not need to be complicated.
It needs to be visible. It needs to be continuous. And it needs to be smart.
If your company depends on APIs, then protecting them is not optional.
It is essential.