Modern applications rely heavily on secrets such as API keys, database passwords, encryption keys, and service account credentials. Managing these secrets securely is critical for protecting systems from breaches, insider threats, and accidental leaks. As organizations scale across cloud and hybrid environments, manually storing secrets in configuration files or environment variables is no longer sufficient. This is where secrets management applications like AWS Secrets Manager and similar tools play a vital role in securely storing, accessing, and rotating credentials.
TLDR: Secrets management apps like AWS Secrets Manager help organizations securely store, access, and automatically rotate sensitive credentials. They reduce the risk of breaches by eliminating hard-coded secrets and enforcing strict access controls. Popular alternatives include HashiCorp Vault, Azure Key Vault, Google Secret Manager, and others. Choosing the right solution depends on infrastructure, compliance needs, and automation requirements.
Secrets management tools are designed to centralize sensitive information, enforce strict access policies, and automate rotation processes to minimize risk. Instead of embedding secrets directly into codebases or configuration files, developers retrieve them securely at runtime using authenticated and authorized APIs. This practice significantly reduces the attack surface and simplifies compliance.
Why Secrets Management Matters
Data breaches frequently occur due to compromised credentials. Hard-coded passwords and API keys stored in repositories — especially public ones — are common entry points for attackers. Once exposed, attackers can move laterally across systems if secrets are reused or poorly secured.
Secrets management solutions address these risks by:
- Centralizing secret storage in encrypted vaults
- Automating credential rotation to reduce exposure windows
- Providing granular access control through IAM policies
- Auditing and logging secret usage for compliance and visibility
- Integrating with DevOps pipelines and cloud-native tools
By moving away from static credentials and toward dynamic, short-lived secrets, organizations significantly strengthen their security posture.
How AWS Secrets Manager Works
AWS Secrets Manager is a fully managed cloud service that securely stores secrets and automatically rotates them using AWS Lambda functions. It integrates tightly with AWS services such as RDS, IAM, and CloudTrail.
Its core features include:
- Encryption at rest using AWS KMS
- Fine-grained access control via IAM policies
- Built-in rotation support for databases
- Audit logging through AWS CloudTrail
- Secure retrieval through SDKs and CLI
Developers retrieve secrets programmatically rather than embedding credentials directly in application code. Rotation reduces the lifespan of exposed credentials, limiting potential damage from compromise.
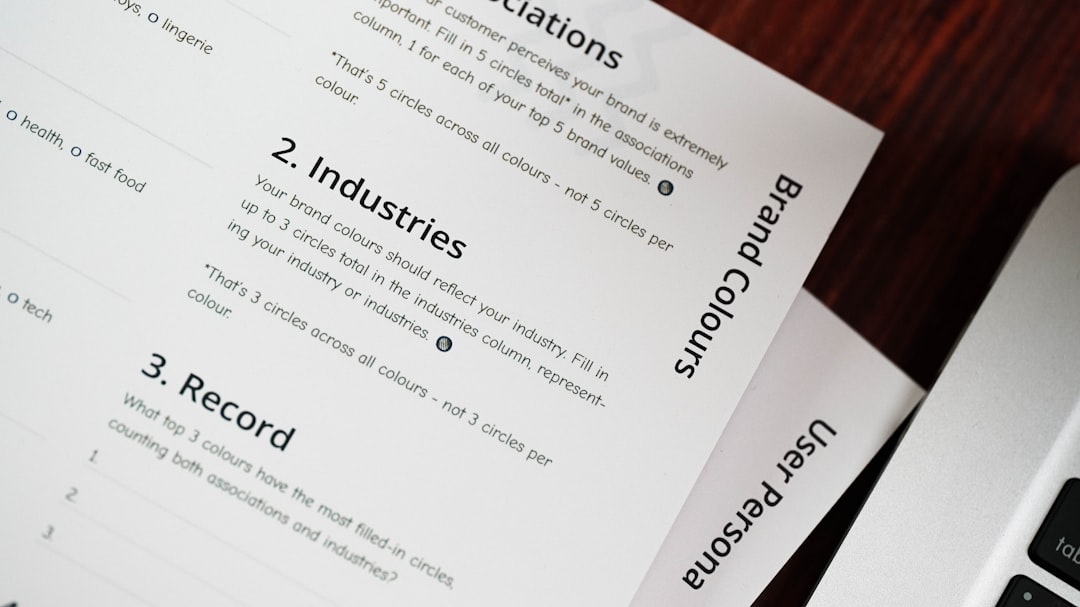
Image not found in postmetaTop Secrets Management Apps Like AWS Secrets Manager
While AWS Secrets Manager is popular among AWS users, several other powerful solutions offer similar or expanded functionality. Below are leading alternatives.
1. HashiCorp Vault
HashiCorp Vault is a widely adopted open-source secrets management tool designed for multi-cloud, hybrid, and on-prem environments. It offers dynamic secrets generation, encryption as a service, and detailed access controls.
Key strengths:
- Platform-agnostic deployment
- Dynamic secret generation
- Extensive secrets engines
- Strong support for zero trust architecture
Vault is particularly suitable for enterprises with complex, multi-cloud infrastructures.
2. Azure Key Vault
Azure Key Vault is Microsoft’s cloud-native solution for securing secrets, keys, and certificates. It integrates deeply with Azure Active Directory and Azure services, making it a natural choice for organizations operating primarily in Microsoft ecosystems.
Key strengths:
- Native Azure integration
- Role-based access control
- Hardware security module (HSM) support
- Certificate lifecycle management
3. Google Secret Manager
Google Secret Manager is built for Google Cloud workloads, offering seamless integration with IAM and Cloud Functions. It focuses on simplicity and secure access within the Google Cloud environment.
Key strengths:
- Automatic replication
- Strong IAM integration
- Versioned secrets management
- Audit logging through Cloud Audit Logs
4. CyberArk Conjur
CyberArk Conjur focuses on enterprise and DevOps security, offering Kubernetes-native integrations and strong authentication mechanisms. It is particularly popular in regulated industries.
Key strengths:
- Kubernetes integration
- Enterprise-grade controls
- Compliance-focused features
- Centralized policy management
Comparison Chart
| Tool | Best For | Automatic Rotation | Multi-Cloud Support | Open Source Option |
|---|---|---|---|---|
| AWS Secrets Manager | AWS environments | Yes | Limited | No |
| HashiCorp Vault | Hybrid and multi-cloud | Yes | Yes | Yes |
| Azure Key Vault | Microsoft Azure users | Partial | Limited | No |
| Google Secret Manager | Google Cloud users | Yes | Limited | No |
| CyberArk Conjur | Enterprise DevOps | Yes | Yes | Community Edition Available |

Key Features to Look for in a Secrets Management App
When evaluating solutions, organizations should consider several critical capabilities:
1. Automatic Secret Rotation
Automatic rotation ensures passwords and API tokens change periodically without manual intervention. This drastically reduces risk exposure.
2. Fine-Grained Access Control
Access should follow the principle of least privilege. Role-based or attribute-based access helps enforce tight security policies.
3. Dynamic Secret Generation
Tools like Vault generate credentials on demand that expire automatically. This eliminates long-lived credentials and enhances security.
4. Audit Logging and Monitoring
Complete visibility into who accessed which secret and when is essential for compliance and forensic investigations.
5. Integration with DevOps and CI/CD Pipelines
Modern development pipelines must securely fetch secrets without exposing them in logs or environment files.
How Automatic Rotation Improves Security
Credential rotation changes passwords, API keys, or tokens at defined intervals. Without automation, teams often delay rotation because of operational complexity.
Automated systems:
- Generate new credentials
- Update target systems (databases, services)
- Invalidate old credentials
- Update applications seamlessly
This process reduces the time window during which compromised credentials remain valid. It also removes dependency on individuals remembering to rotate secrets manually.
Cloud-Native vs. Platform-Agnostic Solutions
Cloud-native tools like AWS Secrets Manager, Azure Key Vault, and Google Secret Manager are optimized for their respective ecosystems. They offer seamless integration, lower operational overhead, and simplified setup.
Platform-agnostic tools like HashiCorp Vault or CyberArk Conjur offer broader deployment flexibility, making them ideal for organizations operating across multiple cloud providers or maintaining significant on-prem infrastructure.
Choosing between them depends on architecture:
- Single-cloud strategy: Native solutions often suffice.
- Multi-cloud or hybrid approach: Platform-agnostic tools provide consistency.
- Strict compliance requirements: Enterprise solutions may offer better governance controls.
Common Implementation Best Practices
Deploying a secrets management system requires more than installing software. Organizations should follow proven best practices:
- Remove hard-coded secrets from source code immediately.
- Adopt short-lived or dynamic credentials whenever possible.
- Implement role-based access control and least privilege policies.
- Enable logging and regularly review audit trails.
- Integrate secret retrieval directly into application runtime.
Additionally, security teams should conduct regular reviews to ensure expired credentials are properly revoked and unused secrets are deleted.
The Future of Secrets Management
As zero trust architectures become more common, secrets management will continue evolving toward identity-based access and ephemeral credentials. Instead of simply rotating static secrets, systems will increasingly rely on temporary identity tokens tied to machine identity and workload context.
Automation, integration with identity providers, and stronger encryption standards will further strengthen the security landscape. Organizations that invest in modern secrets management today position themselves for a more resilient and compliant future.
FAQ
1. What is a secrets management app?
A secrets management app securely stores and controls access to sensitive data such as passwords, API keys, certificates, and encryption keys. It centralizes secret storage and helps automate credential rotation.
2. Why is automatic rotation important?
Automatic rotation reduces the lifespan of credentials. If a secret is compromised, its validity period is limited, reducing the attack window.
3. Is AWS Secrets Manager only for AWS services?
While designed for AWS environments, it can manage credentials for external services as well. However, it is most effective when integrated within the AWS ecosystem.
4. What is the difference between secrets management and encryption?
Encryption protects data by converting it into unreadable form. Secrets management focuses on securely storing, accessing, rotating, and auditing sensitive credentials.
5. Can small businesses benefit from secrets management tools?
Yes. Even small teams handle sensitive data. Automated tools reduce human error and simplify security practices regardless of company size.
6. Which tool is best for multi-cloud environments?
HashiCorp Vault and CyberArk Conjur are strong choices for multi-cloud and hybrid deployments due to their platform-agnostic design.
7. How often should secrets be rotated?
Rotation frequency depends on risk level and compliance requirements, but many organizations rotate critical credentials every 30 to 90 days or use dynamic secrets that expire within hours.